
Sc-100 Microsoft Cybersecurity Architect Course With Sims
Published 4/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 12.17 GB | Duration: 18h 24m
Get prepared for the SC-100 exam with instructor led labs and hands on simulations available 24/7
[b]What you'll learn[/b]
Learn the concepts and perform hands on activities needed to pass the SC-100 exam
Gain a tremendous amount of knowledge involving securing Microsoft 365 and Azure Services
Get loads of hands on experience with Microsoft Cybersecurity for Azure and Microsoft 365
Utilize hands on simulations that can be accessed anytime, anywhere!
[b]Requirements[/b]
Willingness to put in the time and practice the steps shown in the course
[b]Description[/b]
We really hope you'll agree, this training is way more then the average course on Udemy! Have access to the following:Training from an instructor of over 20 years who has trained thousands of people and also a Microsoft Certified TrainerLecture that explains the concepts in an easy to learn method for someone that is just starting out with this materialInstructor led hands on and simulations to practice that can be followed even if you have little to no experienceTOPICS COVERED INCLUDING HANDS ON LECTURE AND PRACTICE TUTORIALS:Design a resiliency strategy for ransomware & other attacks based on MS Security Working with business resiliency goals, identifying and prioritizing threatsMS ransomware best practices, including backup, restore, and privileged accessSecure backup and restore by using Azure BackupSecurity updates using the Azure Update ManagerDesign solutions that align with the MCRA and MCSBConcepts of cybersecurity capabilities and controls using Zero Trust securityConcepts of MS Defender for protecting against insider and external attacksNavigating the Microsoft Defender and Microsoft Purview admin centersUnderstanding insider risk policies as a mitigation solution Implementing insider risk management policies in Microsoft Purview Using the Zero Trust Rapid Modernization Plan (RaMP) as your security strategyDesign solutions that align with the Microsoft CAF and WAF FrameworksSecurity and governance based on Microsoft Cloud Adoption Framework (CAF)Security and governance based on Microsoft Azure Well-Architected FrameworkUsing Azure landing zones for implementing and governing securityThe DevSecOps process modelDesign solutions for security operationsSecurity operations capabilities to support a hybrid or multicloud environmentRequirements for centralized logging and auditing Setting audit permissions and enabling support Perform threat hunting by with audit logging Understanding the Kusto Query Language (KQL) for use in threat hunting Detection and response concepts of extended detection and response (XDR) Confirming we understand the concept of Microsoft Sentinel Setting up a Log Analytics workspace and Microsoft Sentinel workspace Confirming we understand the concepts of SIEM and SOAR Visualizing data ingestion for use in Microsoft Sentinel Understanding analytic rules in Microsoft Sentinel to support SIEM and SOAR Workflow for creating security analytic rules for incident response & management Workflow for creating built-in scheduled query rules Workflow for creating near-real-time (NRT) analytics rules Automation with security orchestration automated response (SOAR) Utilizing content gallery hunting queries for threat hunting Threat detection coverage by using MITRE ATT&CK Design solutions for identity and access managementUnderstanding SaaS, PaaS, and IaaS, & how it relates to Azure hybrid/on-premise Use cases with SaaS, PaaS, & IaaS including identity, networking, applications External identities, business-to-business (B2B), & business-to-customer (B2C)Managing business-to-business (B2B) settings within Entra IDUsing Entra ID external identities for a business-to-business (B2B) solutionCreating a tenant for using business-to-customer (B2C) scenariosDecentralized identities with the help of Microsoft Entra Verified IDThreat mitigation with sign-in logs in Microsoft Entra IDUnderstanding Entra Identity Protection for continuous access evaluationUsing Entra Identity Protection for securing authentication and authorizationThreat intelligence integration from Entra Identity Protection into MS DefenderUnderstanding Multi Factor Authentication (MFA)Implementing Muti Factor Authentication in Microsoft Entra IDImplementing Self Service Password Reset (SSPR) in Microsoft Entra IDUnderstanding Conditional Access Policies with a Zero Trust strategyImplementing Conditional Access Policies with a Zero Trust strategyConcepts of threat intelligence integration with Defender for Cloud Design and configure workflow automation in Microsoft Defender for CloudSetting up email notifications within Defender for CloudCreate and manage alert suppression rulesGenerate sample alerts and incidents in Microsoft Defender for CloudRemediate alerts and incidents by using MS Defender for Cloud recommendationsManage security alerts and incidentsAnalyze Microsoft Defender for Cloud threat intelligence reportsConcepts of securing the various types of identities using Defender for IdentityHybrid Active Directory Domain Services (ADDS) connections for secure identitiesCreating an Azure Key Vault for secrets, keys, and certificates Access control to secrets, keys, and certificates with Azure Key Vault Managing secrets, keys, and certificates with Azure Key vault Removing key vault servicesDesign solutions for securing privileged accessAssigning and delegating privileged roles by using the enterprise access modelUnderstanding RBAC for Identity governance & privileged access managementImplementing RBAC to provide privileged access management in Entra ID & AzureCreating a custom RBAC role in Microsoft Entra IDUsing RBAC to provide access to Azure resourcesImplementing RBAC to provide privileged access management in Microsoft 365Understanding Microsoft Entra Privileged Identity Management (PIM)Implementing Microsoft Entra Privileged Identity Management (PIM)Understanding entitlement management as an identity governance solutionCreating catalogs for entitlement managementImplementing entitlement management with Microsoft Entra Permissions ManagementUser access request entitlement management to an access packageIdentity governance with access reviews in Microsoft EntraPrivileged Access Workstation (PAW) and bastion servicesDesign solutions for regulatory complianceDetermining compliance requirements for security solution adaptationSolutions that address compliance requirements by using Microsoft PurviewUtilizing Microsoft Priva for privacy requirementsCreating Privacy Risk Management policies to meet privacy requirementsAzure Policy solutions to address security and compliance requirementsCompliance with Microsoft Defender for CloudDesign solutions for security posture management in hybrid and multicloudSecurity posture with regulatory compliance policies and MCSB Security posture with Microsoft Defender for CloudSecurity posture with Microsoft Secure ScoreEnabling support for Defender for servers within Defender for Cloud Enabling Microsoft Defender for Servers as a cloud workload protection solutionEnabling Microsoft Defender for App Service as a cloud app protection solutionIntegration with hybrid and multicloud environments by using Azure Arc Support for Microsoft Defender for DevOps within Defender for CloudUtilizing Microsoft Defender External Attack Surface Management (Defender EASM) Design solutions for securing server and client endpointsUsing Microsoft Defender for Endpoint for securing multiple platforms and OS' Configuring settings in Microsoft Defender for Endpoint Utilizing Microsoft Intune for mobile devices & client for endpoint protection Managing security requirements on mobile devices & clients endpoints with Intune Using security baselines to secure servers and client endpointsIoT, OT and ICS security discovery using Microsoft Defender for IoTSecure remote access with Microsoft Entra Global Secure AccessSpecify requirements for securing SaaS, PaaS, and IaaS servicesSecurity baselines for SaaS, PaaS, and IaaS servicesSecurity in your IoT workloadsWeb workload management with Azure App Service plans Creating an Azure App Service plan Adding an App Service for web workloads Securing web workloads with Azure App ServicesUnderstanding containers in Azure Creating a container instance in Azure Securing Azure container instancesContainer orchestration with Azure Kubernetes Service (AKS) Scaling container orchestration with Azure Kubernetes Service (AKS) Securing container orchestration with Azure Kubernetes Service (AKS)Design solutions for securing Microsoft 365Posture with Microsoft Secure Score & Microsoft Defender for Cloud secure scoreRequirements for a Microsoft 365 Defender security solutionSecure configuration & operational practices for Microsoft 365 workloads & dataDesign solutions for securing applicationsSecuring existing application portfolios and business-critical applicationsStandards and practices for securing the application development processConsiderations for API management and security solutionsUnderstanding secure access with Azure Web Application Firewall (WAF) Use cases for implementing the Azure Front Door Setting up an Azure Web Application Firewall (WAF) & Azure Front Door Removing existing resources up to this pointDesign solutions for securing an organization's dataUnderstanding data discovery and classification with Purview sensitivity labels Managing sensitive info types for a classification data governance solution Implementing a data governance & classification solution with sensitivity labelsVisualizing protection solutions with data at rest, data in motion & data in useUnderstanding the concepts of relational databases Setting up an Azure SQL database and connecting with SSMS Configuring Azure SQL firewall settings for client connectionsUtilizing Azure SQL dynamic maskingUtilizing Azure SQL database encryption Understanding the concepts of non-relational data and NoSQL Setting up an Azure Cosmos DB solution in Azure Protection and durability with replication of an Azure Cosmos DB Remove existing database resourcesGrasping the purposes of Azure Synapse Analytics Registering Azure Synapse as a resource provider Creating a SQL DB and server for use with Azure Synapse Analytics Adding an Azure Synapse workspace and Data Lake Storage account Visualizing the concepts of SQL Pool usage with Azure Synapse Analytics Setting up a SQL Pool for usage with Azure Synapse Confirming we understand the concepts of Azure Storage accounts Creating an Azure Storage account as a data storage solutionMitigating threats to data within our Azure Storage account solutionEnabling Defender for Storage within a Azure Storage accountUtilizing Microsoft Defender for SQL as a security solution ConclusionCleaning up resourceGetting a Udemy certificateBONUS Where do I go from here?
Overview
Section 1: Introduction
Lecture 1 Welcome to the SC-100 course!
Lecture 2 Understanding the Microsoft Environment
Lecture 3 Foundations of Active Directory Domains
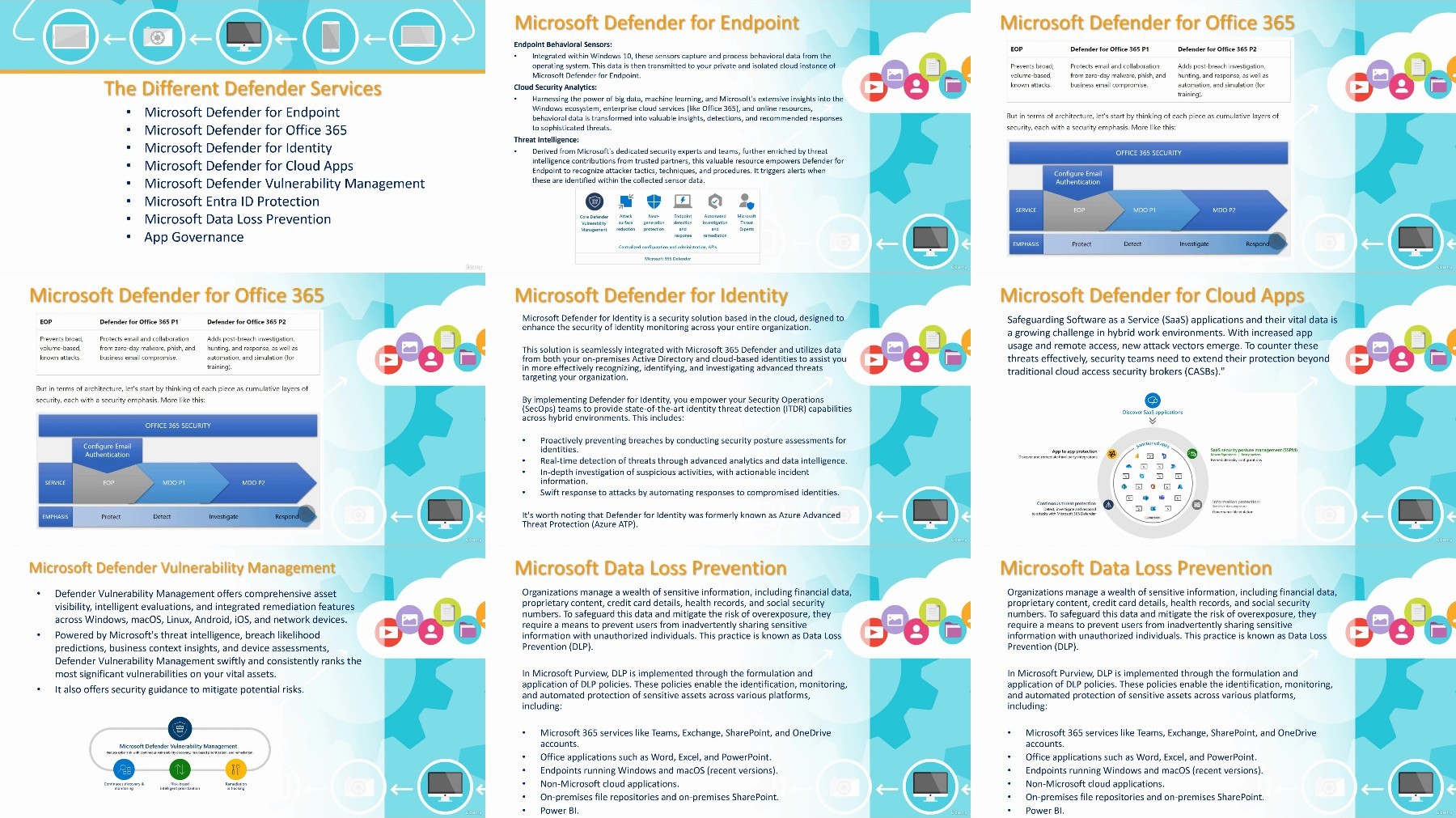
Lecture 4 Foundations of RAS, DMZ, and Virtualization
Lecture 5 Foundations of the Microsoft Cloud Services
Lecture 6 DONT SKIP: The first thing to know about Microsoft cloud services
Lecture 7 DONT SKIP: Azure AD is now renamed to Entra ID
Lecture 8 Questions for John Christopher
Lecture 9 Order of concepts covered in the course
Lecture 10 Overlap with other certifications
Section 2: Performing hands on activities
Lecture 11 DONT SKIP: Using Assignments/Simulations in the course
Lecture 12 Creating a free Microsoft 365 Account
Lecture 13 Getting your free Azure credit
Section 3: Design a resiliency strategy for ransomware & other attacks based on MS Security
Lecture 14 Working with business resiliency goals, identifying and prioritizing threats
Lecture 15 MS ransomware best practices, including backup, restore, and privileged access
Lecture 16 Secure backup and restore by using Azure Backup
Lecture 17 Security updates using the Azure Update Manager
Section 4: Design solutions that align with the MCRA and MCSB
Lecture 18 Concepts of cybersecurity capabilities and controls using Zero Trust security
Lecture 19 Concepts of MS Defender for protecting against insider and external attacks
Lecture 20 Navigating the Microsoft Defender and Microsoft Purview admin centers
Lecture 21 Understanding insider risk policies as a mitigation solution
Lecture 22 Implementing insider risk management policies in Microsoft Purview
Lecture 23 Using the Zero Trust Rapid Modernization Plan (RaMP) as your security strategy
Section 5: Design solutions that align with the Microsoft CAF and WAF Frameworks
Lecture 24 Security and governance based on Microsoft Cloud Adoption Framework (CAF)
Lecture 25 Security and governance based on Microsoft Azure Well-Architected Framework
Lecture 26 Using Azure landing zones for implementing and governing security
Lecture 27 The DevSecOps process model
Section 6: Design solutions for security operations
Lecture 28 Security operations capabilities to support a hybrid or multicloud environment
Lecture 29 Requirements for centralized logging and auditing
Lecture 30 Setting audit permissions and enabling support
Lecture 31 Perform threat hunting by with audit logging
Lecture 32 Understanding the Kusto Query Language (KQL) for use in threat hunting
Lecture 33 Detection and response concepts of extended detection and response (XDR)
Lecture 34 Confirming we understand the concept of Microsoft Sentinel
Lecture 35 Setting up a Log Analytics workspace and Microsoft Sentinel workspace
Lecture 36 Confirming we understand the concepts of SIEM and SOAR
Lecture 37 Visualizing data ingestion for use in Microsoft Sentinel
Lecture 38 Understanding analytic rules in Microsoft Sentinel to support SIEM and SOAR
Lecture 39 Workflow for creating security analytic rules for incident response & management
Lecture 40 Workflow for creating built-in scheduled query rules
Lecture 41 Workflow for creating near-real-time (NRT) analytics rules
Lecture 42 Automation with security orchestration automated response (SOAR)
Lecture 43 Utilizing content gallery hunting queries for threat hunting
Lecture 44 Threat detection coverage by using MITRE ATT&CK
Section 7: Design solutions for identity and access management
Lecture 45 Understanding SaaS, PaaS, and IaaS, & how it relates to Azure hybrid/on-premise
Lecture 46 Use cases with SaaS, PaaS, & IaaS including identity, networking, applications
Lecture 47 External identities, business-to-business (B2B), & business-to-customer (B2C)
Lecture 48 Managing business-to-business (B2B) settings within Entra ID
Lecture 49 Using Entra ID external identities for a business-to-business (B2B) solution
Lecture 50 Creating a tenant for using business-to-customer (B2C) scenarios
Lecture 51 Decentralized identities with the help of Microsoft Entra Verified ID
Lecture 52 Threat mitigation with sign-in logs in Microsoft Entra ID
Lecture 53 Understanding Entra Identity Protection for continuous access evaluation
Lecture 54 Using Entra Identity Protection for securing authentication and authorization
Lecture 55 Threat intelligence integration from Entra Identity Protection into MS Defender
Lecture 56 Understanding Multi Factor Authentication (MFA)
Lecture 57 Implementing Muti Factor Authentication in Microsoft Entra ID
Lecture 58 Implementing Self Service Password Reset (SSPR) in Microsoft Entra ID
Lecture 59 Understanding Conditional Access Policies with a Zero Trust strategy
Lecture 60 Implementing Conditional Access Policies with a Zero Trust strategy
Lecture 61 Concepts of threat intelligence integration with Defender for Cloud
Lecture 62 Design and configure workflow automation in Microsoft Defender for Cloud
Lecture 63 Setting up email notifications within Defender for Cloud
Lecture 64 Create and manage alert suppression rules
Lecture 65 Generate sample alerts and incidents in Microsoft Defender for Cloud
Lecture 66 Remediate alerts and incidents by using MS Defender for Cloud recommendations
Lecture 67 Manage security alerts and incidents
Lecture 68 Analyze Microsoft Defender for Cloud threat intelligence reports
Lecture 69 Concepts of securing the various types of identities using Defender for Identity
Lecture 70 Hybrid Active Directory Domain Services (ADDS) connections for secure identities
Lecture 71 Creating an Azure Key Vault for secrets, keys, and certificates
Lecture 72 Access control to secrets, keys, and certificates with Azure Key Vault
Lecture 73 Managing secrets, keys, and certificates with Azure Key vault
Lecture 74 Removing key vault services
Section 8: Design solutions for securing privileged access
Lecture 75 Assigning and delegating privileged roles by using the enterprise access model
Lecture 76 Understanding RBAC for Identity governance & privileged access management
Lecture 77 Implementing RBAC to provide privileged access management in Entra ID & Azure
Lecture 78 Creating a custom RBAC role in Microsoft Entra ID
Lecture 79 Using RBAC to provide access to Azure resources
Lecture 80 Implementing RBAC to provide privileged access management in Microsoft 365
Lecture 81 Understanding Microsoft Entra Privileged Identity Management (PIM)
Lecture 82 Implementing Microsoft Entra Privileged Identity Management (PIM)
Lecture 83 Understanding entitlement management as an identity governance solution
Lecture 84 Creating catalogs for entitlement management
Lecture 85 Implementing entitlement management with Microsoft Entra Permissions Management
Lecture 86 User access request entitlement management to an access package
Lecture 87 Identity governance with access reviews in Microsoft Entra
Lecture 88 Privileged Access Workstation (PAW) and bastion services
Section 9: Design solutions for regulatory compliance
Lecture 89 Determining compliance requirements for security solution adaptation
Lecture 90 Solutions that address compliance requirements by using Microsoft Purview
Lecture 91 Utilizing Microsoft Priva for privacy requirements
Lecture 92 Creating Privacy Risk Management policies to meet privacy requirements
Lecture 93 Azure Policy solutions to address security and compliance requirements
Lecture 94 Compliance with Microsoft Defender for Cloud
Section 10: Design solutions for security posture management in hybrid and multicloud
Lecture 95 Security posture with regulatory compliance policies and MCSB
Lecture 96 Security posture with Microsoft Defender for Cloud
Lecture 97 Security posture with Microsoft Secure Score
Lecture 98 Enabling support for Defender for servers within Defender for Cloud
Lecture 99 Enabling Microsoft Defender for Servers as a cloud workload protection solution
Lecture 100 Enabling Microsoft Defender for App Service as a cloud app protection solution
Lecture 101 Integration with hybrid and multicloud environments by using Azure Arc
Lecture 102 Support for Microsoft Defender for DevOps within Defender for Cloud
Lecture 103 Utilizing Microsoft Defender External Attack Surface Management (Defender EASM)
Section 11: Design solutions for securing server and client endpoints
Lecture 104 Using Microsoft Defender for Endpoint for securing multiple platforms and OS'
Lecture 105 Configuring settings in Microsoft Defender for Endpoint
Lecture 106 Utilizing Microsoft Intune for mobile devices & client for endpoint protection
Lecture 107 Managing security requirements on mobile devices & clients endpoints with Intune
Lecture 108 Using security baselines to secure servers and client endpoints
Lecture 109 IoT, OT and ICS security discovery using Microsoft Defender for IoT
Lecture 110 Secure remote access with Microsoft Entra Global Secure Access
Section 12: Specify requirements for securing SaaS, PaaS, and IaaS services
Lecture 111 Security baselines for SaaS, PaaS, and IaaS services
Lecture 112 Security in your IoT workloads
Lecture 113 Web workload management with Azure App Service plans
Lecture 114 Creating an Azure App Service plan
Lecture 115 Adding an App Service for web workloads
Lecture 116 Securing web workloads with Azure App Services
Lecture 117 Understanding containers in Azure
Lecture 118 Creating a container instance in Azure
Lecture 119 Securing Azure container instances
Lecture 120 Container orchestration with Azure Kubernetes Service (AKS)
Lecture 121 Scaling container orchestration with Azure Kubernetes Service (AKS)
Lecture 122 Securing container orchestration with Azure Kubernetes Service (AKS)
Section 13: Design solutions for securing Microsoft 365
Lecture 123 Posture with Microsoft Secure Score & Microsoft Defender for Cloud secure score
Lecture 124 Requirements for a Microsoft 365 Defender security solution
Lecture 125 Secure configuration & operational practices for Microsoft 365 workloads & data
Section 14: Design solutions for securing applications
Lecture 126 Securing existing application portfolios and business-critical applications
Lecture 127 Standards and practices for securing the application development process
Lecture 128 Considerations for API management and security solutions
Lecture 129 Understanding secure access with Azure Web Application Firewall (WAF)
Lecture 130 Use cases for implementing the Azure Front Door
Lecture 131 Setting up an Azure Web Application Firewall (WAF) & Azure Front Door
Lecture 132 Removing existing resources up to this point
Section 15: Design solutions for securing an organization's data
Lecture 133 Understanding data discovery and classification with Purview sensitivity labels
Lecture 134 Managing sensitive info types for a classification data governance solution
Lecture 135 Implementing a data governance & classification solution with sensitivity labels
Lecture 136 Visualizing protection solutions with data at rest, data in motion & data in use
Lecture 137 Understanding the concepts of relational databases
Lecture 138 Setting up an Azure SQL database and connecting with SSMS
Lecture 139 Configuring Azure SQL firewall settings for client connections
Lecture 140 Utilizing Azure SQL dynamic masking
Lecture 141 Utilizing Azure SQL database encryption
Lecture 142 Understanding the concepts of non-relational data and NoSQL
Lecture 143 Setting up an Azure Cosmos DB solution in Azure
Lecture 144 Protection and durability with replication of an Azure Cosmos DB
Lecture 145 Remove existing database resource
Lecture 146 Grasping the purposes of Azure Synapse Analytics
Lecture 147 Registering Azure Synapse as a resource provider
Lecture 148 Creating a SQL DB and server for use with Azure Synapse Analytics
Lecture 149 Adding an Azure Synapse workspace and Data Lake Storage account
Lecture 150 Visualizing the concepts of SQL Pool usage with Azure Synapse Analytics
Lecture 151 Setting up a SQL Pool for usage with Azure Synapse
Lecture 152 Confirming we understand the concepts of Azure Storage accounts
Lecture 153 Creating an Azure Storage account as a data storage solution
Lecture 154 Mitigating threats to data within our Azure Storage account solution
Lecture 155 Enabling Defender for Storage within a Azure Storage account
Lecture 156 Utilizing Microsoft Defender for SQL as a security solution
Section 16: Conclusion
Lecture 157 Removing all resources
Lecture 158 Getting a Udemy certificate
Lecture 159 BONUS - Where to go from here
IT people interested in learning and passing the Microsoft SC-100 Exam,People interested in learning a tremendous amount about Microsoft Cybersecurity for Azure and Microsoft 365
https://ddownload.com/4qko3tb6fzkm/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part1.rar https://ddownload.com/ap2yt265pnjr/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part2.rar https://ddownload.com/nnwpztgqphni/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part3.rar https://ddownload.com/2vci9v6mm46h/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part4.rar https://ddownload.com/8t7lqw7f47os/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part5.rar https://ddownload.com/7lfe919d8jha/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part6.rar https://ddownload.com/36aiyc6myao9/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part7.rar
https://rapidgator.net/file/7846714a0ebb2dab53b90614cb46e26f/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part1.rar https://rapidgator.net/file/af26fcfece2f7298a98634d58b34a5e5/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part2.rar https://rapidgator.net/file/4f63c2712bc88f69a18189fd3de4ecd2/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part3.rar https://rapidgator.net/file/360668ff0b361bfe7265823df539a20d/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part4.rar https://rapidgator.net/file/30726b79df8bcb69aa4dbddbfe8fde55/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part5.rar https://rapidgator.net/file/eb7c72212cec618ef3741bdfc943439a/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part6.rar https://rapidgator.net/file/af1deb4935b7e4169fe34096531412ca/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part7.rar
https://turbobit.net/xmtjry3lh00j/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part1.rar.html https://turbobit.net/xdqbuzse261x/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part2.rar.html https://turbobit.net/t2t9awfckkgk/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part3.rar.html https://turbobit.net/hxpz1d9o3nii/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part4.rar.html https://turbobit.net/tx1l29f9ok10/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part5.rar.html https://turbobit.net/jnk84lu7q7a1/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part6.rar.html https://turbobit.net/ms87e7ep17nt/Udemy_SC-100_Microsoft_Cybersecurity_Architect_course_with_sims.part7.rar.html

